If you’re in security, you’ve noticed the flood of AI-powered penetration testing tools hitting the market. Some of them are doing genuinely impressive work: chaining exploits, reasoning about application behavior, and finding potential vulnerabilities that vulnerability scanners have missed for years. Others are wrappers around ChatGPT with a landing page and a waitlist.
We’ve been tracking how AI is reshaping application security at StackHawk, and pentesting is one of the areas where the impact is most visible. But most content misses where AI pen testing provides value, and where it actually slows things down.
That said, the shift from legacy scanning to AI-powered testing isn’t a clean replacement. At StackHawk, we love seeing the innovation in this area, leveraging AI to make manual tasks faster and cheaper. We do not, however, see AI pentesting as a replacement for deterministic (even if AI-supported) DAST (Dynamic Application Security Testing) that can run fast enough to surface vulnerabilities to developers in context so they can actually fix them. None of these tools replace DAST, but we are seeing that the best security programs combine periodic AI pentesting with continuous DAST in their pipeline.
Here’s our take on where different AI pentesting vendors thrive, because not all tools are created equal: some are strong at certain vulnerability classes and weak at others. If you’re evaluating these automated tools for your security posture, you need to know both sides. We’ll break down the tools worth your time, explain what they do well, and show where they leave gaps that other tools need to fill.
TL;DR
- Horizon3 (NodeZero): Best for autonomous network pentesting
- PentestGPT: Best free, open source starting point
- Penligent: Agentic AI with 200+ tool orchestration
- HackerAI: AI-assisted pentest workflows for consultants
- Escape: Business logic testing with agentic exploit reasoning
- XBOW: Most advanced autonomous exploit validation
What Is AI-Powered Penetration Testing?
AI penetration testing uses artificial intelligence, machine learning, and large language models to automate what traditional penetration testing focuses on manually: reconnaissance, vulnerability discovery, exploit development, and reporting. Instead of an ethical hacker probing your web application one endpoint at a time, an AI agent handles the repetitive grind and surfaces findings for human review.
The “AI” part matters because traditional vulnerability scanners follow deterministic, predefined rules. They check for known vulnerabilities and run signature-based tests. AI pentesting tools reason about an application’s behavior, chain vulnerabilities together, and adapt their strategy based on what they find. They often leverage industry tools such as Nmap, StackHawk, Metasploit, and OWASP ZAP to orchestrate attacks via AI agents that decide which tool to use at each stage of an engagement, much like a human pentester would.
How AI Pentesting Tools Work, at a high level
Most AI pentesting tools follow a similar workflow, even if the implementation details vary.

AI-Augmented Reconnaissance
Traditional recon means running Nmap, Shodan queries, and subdomain enumeration scripts, then manually piecing together the results. AI tools automate all of that, then correlate results across sources to catch patterns humans miss, operating at machine speed. These tools can do things like achieve full Domain Admin access in under 60 seconds, compromise a bank’s core systems in under 4 minutes, and test over 100,000 IP addresses in a single autonomous run. Helping to identify attack paths that manual techniques would have taken days to map.
Autonomous Exploit Discovery
This is where AI pen testing tools pull ahead of traditional scanners. Rather than matching signatures against a database, these AI models analyze application behavior, identify logical flaws, and attempt to chain low-severity findings into high-impact exploit paths that simulate real-world attacks. XBOW validates every potential finding through real-world exploitation, not theoretical risk scoring. Escape uses reinforcement learning combined with generative AI to build exploit chains specific to the application it’s testing.
Human-in-the-Loop Validation
No serious AI pentesting tool operates fully autonomously without oversight. The best tools present findings with proof-of-concept exploits and then let pen testers validate, prioritize, and expand on the results. The AI handles volume. Human testers add judgment and context that AI systems lack. Penligent makes this explicit with customizable prompts and a CLI-based workflow that keeps the tester in control of scope and escalation decisions.
Open Source vs. Commercial AI Pentesting Tools
The open source AI pentesting ecosystem is growing, but it’s still early.
Open source tools (PentestGPT, Garak, BugTrace-AI) give you flexibility and code transparency. You can inspect the testing methodology, customize it, and run it without licensing costs. The tradeoff is that you own setup, maintenance, and updates. Most open source options also assume you already know penetration testing. They augment expertise rather than replace it.
Commercial platforms (Horizon3, Penligent, XBOW) handle infrastructure, provide support, and ship more polished user experiences. They’re better suited for organizations that want to deploy AI pentesting as part of an ongoing security program without dedicating engineering time to tool maintenance. Expect to verify that commercial tools mitigate risks around false positives and alert noise before committing.
For most teams, the practical split looks like this: open source for research, learning, and targeted testing; commercial for production security programs. If you’re searching for AI pentesting tools on GitHub, PentestGPT is the best starting point. Horizon3 leads on network and infrastructure scope.
How to Choose the Right AI Pentesting Tool
With so many options, a decision must be made on what to get started with. Not every tool on this list fits every team. Here’s how to think about the decision.
Key Evaluation Criteria
What are you actually testing? Network infrastructure pen testing and web app pentesting require fundamentally different tools. Horizon3 and Penligent focus on network and infrastructure testing. StackHawk focuses on application and API security. Match the tool to your actual attack surface, not the one you think you have. StackHawk’s API discovery can help here by mapping your full API attack surface from source code, including undocumented and shadow web applications you might not know about.
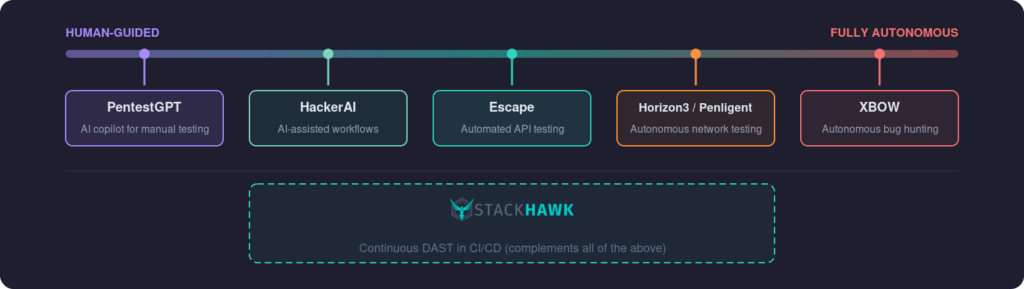
How autonomous do you want the testing to be? Some teams want AI to handle everything with minimal human input. Others want a copilot that assists human testers. This is a maturity question, not just a preference. If your security teams lack the expertise to interpret autonomous tool findings, a more guided approach (PentestGPT, HackerAI) is safer than throwing an autonomous agent at your production environment.
What’s your testing cadence? AI pentesting tools are built for periodic deep assessments. If you need continuous security validation on every code change, you need something that runs in your pipeline. Understanding the difference between DAST and penetration testing matters here: they’re not interchangeable, and most teams benefit from running both.
Can you handle the findings? This is the most common failure mode. Deploying an AI pentesting tool that generates hundreds of findings is counterproductive if your team already spends most of its time triaging alerts. Our 2026 AppSec Survival Guide has data on this problem. Make sure your remediation workflow can absorb what the tool produces before you turn it on.
Integration with Your Security Stack
AI pentesting tools don’t work in isolation. They feed into vulnerability management, ticketing, and CI/CD systems. Before committing to a tool, verify that it integrates with your actual workflow. A tool that dumps findings into a PDF report creates more work than it eliminates.
StackHawk integrates natively with Jira, GitHub, GitLab, Azure DevOps, Slack, and Datadog. The scanner runs inside your CI/CD pipeline, and findings go directly to the developers who can fix them. That’s a different model from tools that produce a report for a security team to manually triage and route.
Best AI Pentesting Tools in 2026
Even though these tools belong to the same class, they still vary quite a bit in their automation.
Let’s put together some of the top platforms so you can see what’s worth your time right now:
| Tool | Type | Key Strength | Best For | Pricing |
| Horizon3.ai (NodeZero) | SaaS | Autonomous network pentesting with proof-of-exploit | Infrastructure and network security | Custom |
| PentestGPT | Open Source | LLM-guided manual pentesting assistant | Individual researchers and CTF players | Free |
| Penligent | SaaS | Agentic AI with 200+ tool orchestration | Organizations wanting autonomous assessments | Custom |
| HackerAI | SaaS | AI-assisted pentest workflows | Security consultants | Freemium |
| Escape | SaaS | Graph-based agentic reasoning for API and web app business logic | Teams with complex auth, BOLA/IDOR exposure testing | Custom |
| XBOW | SaaS | Autonomous exploit validation and chaining | Bug bounty programs and deep assessments | Custom |
Horizon3.ai (NodeZero)
NodeZero is the most mature autonomous pentesting platform available. It runs fully autonomous internal, external, and cloud penetration tests, plus Active Directory password audits and phishing impact assessments. With a track record of 170,000+ tests run in production environments, it’s proven to be production-safe. Horizon3 is particularly strong at credential-based attacks, lateral movement, and validating exposure to emerging threats and exploitable vulnerabilities using CISA KEV data.
Standout feature: Business-impact prioritization with proof-of-exploitation, not just CVSS scores. Their Find-Fix-Verify workflow lets you remediate and immediately retest.
PentestGPT
The open source tool that kicked off the AI pentesting conversation. PentestGPT acts as an interactive assistant for manual pen testing, helping with task planning, suggesting next steps during engagements, and generating payloads. It’s not autonomous, but it makes skilled pen testers faster by handling the cognitive overhead of deciding what to try next.
Standout feature: Free, open source, and actively maintained on GitHub. The best entry point for learning AI-assisted pen testing methodology.
Penligent
Penligent calls itself “the world’s first agentic AI hacker.” It deploys AI agents that orchestrate 200+ industry-standard tools (Nmap, Burp Suite, Metasploit, OWASP ZAP, WhatWeb, searchsploit) to autonomously discover and exploit vulnerabilities specific to each target. The agents adapt their approach based on findings, similar to how an ethical hacker pivots during an engagement. Their CLI-based workflow and customizable prompts keep testers in control while letting the AI handle execution.
Standout feature: Agentic multi-tool orchestration. Their claim is “what takes humans a week, Penligent takes an hour,” backed by detailed pentest reports with severity-classified findings and one-click proof-of-concept generation.
HackerAI
HackerAI positions itself as an AI-powered pentesting assistant with a chat-based interface aimed at security experts and teams running regular assessments. It automates the repetitive parts of pentest engagements: recon, evidence collection, and report generation.
Standout feature: Conversational interface for pentest workflow management. Aimed at consultants who need to move through engagements faster.
Escape
Escape rebranded from API security scanning to a full offensive security platform in early 2026, backed by an $18M Series A. The platform now covers three areas: attack surface management, business-logic-aware DAST, and AI pentesting. The distinction worth paying attention to is how the AI pentesting engine works: it uses graph-based reasoning to model application state across user roles, sessions, and request chains, which makes it effective at surfacing authorization flaws like BOLA and IDOR.
Standout feature: Persistent regression testing from any finding source. Escape converts findings from its own engine, bug bounty programs, or manual pentest reports into permanent regression tests.
XBOW
XBOW takes a different approach. Built for autonomous offensive security, it uses multi-agent execution to run targeted attacks that validate every finding through real-world exploitation, not theoretical risk scoring. XBOW uncovers edge cases and unique vulnerabilities in complex applications that other tools miss by going deep rather than wide. Seznam.cz’s security team noted that after a year, no other company was close to XBOW in agentic pentesting.
Standout feature: Proof-based findings with validated exploit chains. Every vulnerability reported has been confirmed through actual exploitation with reproduction steps.
Where Does StackHawk Fit in All This?
If you were thinking, “Why is StackHawk talking about AI pentesting tools?” you’re asking the right question. We think it’s important to show you how the platforms above and StackHawk can work together.
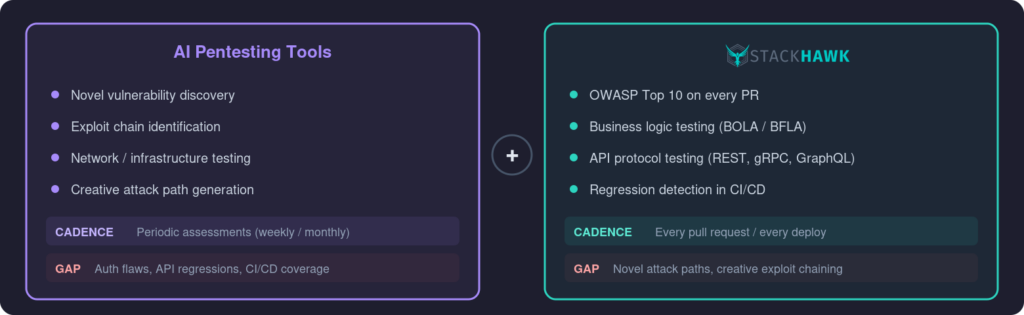
At its core, StackHawk is a DAST platform built to run where developers live (on their local machines and in CI/CD) and uses AI to power API attack surface discovery and remediation guidance. We include it here because AI pentesting tools and DAST solve different but complementary problems, and most security teams need both.
Where AI pentesting tools run periodic assessments and find novel attack paths, StackHawk runs on every pull request and catches regressions, OWASP Top 10 vulnerabilities, and API security issues continuously. The platform uses AI to generate OpenAPI specifications directly from source code, giving security teams full visibility into APIs that lack documentation. Business Logic Testing catches authorization flaws like BOLA and BFLA through automated multi-user auth testing, which addresses a gap that autonomous AI pentesters struggle with: detecting flaws involving sensitive information that only appear across multiple user contexts.
These AI pen testing tools need a partner in crime, something a bit closer to where developers are building, giving real-time security feedback to remediate before it can get picked up in a more periodic pen test (AI-enabled, or not).
The Future of AI in Penetration Testing
Three shifts are coming fast.
Agentic AI is the big one. Testing is moving from scripted workflows to AI agents that reason about security problems and make autonomous decisions about how to exploit them. Penligent and XBOW are early examples of this architecture. Expect every major security vendor to ship agent-based testing within the next 12 to 18 months.
Continuous autonomous testing will blur the line between pentesting and monitoring. Instead of running periodic assessments, organizations will deploy AI agents that probe their applications continuously. That creates real problems around noise and false positives, but the direction is clear. Tools like StackHawk are already doing this for known vulnerability classes through runtime DAST in CI/CD; AI will extend it to novel attack paths.
AI will augment human red teams, not replace them. The pattern across every tool on this list is the same: AI handles volume and repetition, humans handle creativity and judgment. StackHawk’s own LLM security testing capabilities reflect this trend, applying AI to test the AI-powered applications themselves. Teams using both AI and human testers will consistently outperform teams relying on either approach alone.
Conclusion
The pattern across every tool on this list is the same: AI handles reconnaissance, repetition, and scale. Humans handle creativity, context, and judgment. The teams getting the best results aren’t choosing one approach over the other. They’re layering them.
But there’s a gap in that stack that none of these AI pentesting tools close on their own. They run periodic assessments, whether that’s weekly, monthly, or quarterly. Between those assessments, every pull request you merge is untested. Every deploy ships without a security check. That’s where known vulnerabilities, auth flaws, and API regressions slip through.
StackHawk closes that gap. It runs DAST scans inside your CI/CD pipeline on every PR, testing for the OWASP Top 10, business logic flaws like BOLA and BFLA, and API-specific issues across REST, gRPC, JSON-RPC, and GraphQL. It’s not a replacement for deep AI pentesting. It’s the continuous layer that keeps your applications covered between assessments.Interested in understanding more about how StackHawk can work with AI pentesting tools to build a holistic AppSec stack? Watch our latest demo to see the platform running against a real application, or contact our team today to schedule a one-on-one demo.