APIs (Application Programming Interface) are the glue of most applications, making functionalities and data communication possible. Powering everything from mobile and web apps to complex enterprise systems, APIs are the most critical part of modern applications. But as their use explodes, so does their potential to be attacked. An API call that exploits a single API vulnerability can expose sensitive data, disrupt services, or even destroy entire infrastructures.
In this post, we’ll unpack API security and API attack surfaces in a practical and informative way. We’ll define key terms, explore common API attack vectors and the vulnerabilities they prey on, and provide strategies to protect your API ecosystem. Whether you’re an AppSec pro or a developer, understanding and mitigating these risks is crucial to building secure web applications.
Understanding API Security
Before we discuss API attacks and vulnerabilities in detail, let’s establish a solid foundation by defining the core concepts of API security.
What is API Security?
At its core, API security is a set of practices designed to protect APIs from unauthorized access, misuse, and attacks. It encompasses everything from authentication and authorization mechanisms to data encryption and input validation. API security is critical to API development, deployment, and support.
Importance of API Security in Modern Applications
The reliance on APIs makes their security crucial. When an API is compromised, it can impact technical and business operations heavily. When an API attack is successful, organizations can expect:
Data breaches: Exposure of sensitive user information or confidential business data.
Service disruptions: Denial of service attacks or malicious activities can disrupt API availability.
Financial losses: The cost of recovering from a security incident can be substantial.
Reputation damage: A security breach can erode customer trust and harm your brand’s image.
Because of these implications, API security should be a top priority for every organization. Foregoing preventative measures to secure APIs and robust monitoring are risks that shouldn’t be taken. To ensure that APIs are well secured, the first step is to understand your API attack surface. Let’s dig into what that means.
The API Attack Surface
Understanding the API attack surface is like mapping the perimeter of a network. It reveals all the potential entry points where malicious actors might try to breach your defenses. Let’s look at the key components of this critical API security aspect.
Definition of an Attack Surface
In the context of API security, the attack surface area refers to the total sum of all vulnerabilities and weaknesses that could be exploited by attackers. It encompasses both the technical aspects of the API implementation and the surrounding infrastructure.
An API’s attack surface consists of various elements that attackers can target, such as:
Endpoints and Methods: These are the specific URLs and actions (GET, POST, PUT, DELETE, etc.) that clients use to interact with the API. If not properly secured, API calls can be exploited to access sensitive data or manipulate the API’s functionality.
Input Parameters: The data clients send in an API request, such as form fields or query parameters, can be manipulated to inject malicious code or trigger unintended behavior.
Authentication and Authorization: These mechanisms control who can access the API and what they can do. Weak authentication can allow attackers to impersonate legitimate users, while flawed authorization can grant excessive privileges.
Data Storage: The databases and other systems where the API stores data can be targeted for unauthorized access or modification.
Network Infrastructure: The servers, routers, and firewalls that support the API can be attacked to disrupt its availability or intercept data in transit.
The attack surface encapsulates every piece of the API code, implementation, and infrastructure. So how does this relate to API security?
How an Attack Surface Relates to API Security
The concept of the attack surface is fundamental to API security because it highlights that security is not just about protecting a single point of entry. It’s about securing every potential avenue of attack, from endpoints to configuration settings.
By having a holistic understanding of the attack surface, you can:
Prioritize Risks: Identify the most critical vulnerabilities and address them first.
Implement Layered Security: Deploy multiple security mechanisms to create a defense-in-depth strategy.
Continuous Monitoring: Regularly assess all angles of the attack surface for new vulnerabilities and adapt your security measures accordingly.
It’s important to note that the attack surface is not static, so the API security approach needs to be dynamic. This dynamic nature results from API changes to code and infrastructure and new threats emerging. Therefore, education, ongoing vigilance, and proactive security measures are essential to keeping your APIs safe. Next, let’s look closer at API security risks and vulnerabilities.
API Security Risks and Vulnerabilities
API code and infrastructure are complex, leading to a complex attack surface. This diverse attack surface creates numerous security risks and vulnerabilities. Understanding these risks is crucial for prioritizing mitigation efforts and establishing effective security practices. Regarding vulnerabilities, we will look at the OWASP API Top 10 and then dig further into one of the most common areas for security gaps in APIs: authentication and authorization flaws.
OWASP Top 10 API Security Risks (2023)
The Open Web Application Security Project (OWASP) lists the top 10 most critical API security risks. In 2023, OWASP released a new iteration of the list they started in 2019 to align with the latest issues being observed. These include:
Broken Object Level Authorization : Unauthorized access to resources due to insufficient object-level authorization checks.
Broken Authentication : Flaws in authentication mechanisms allowing attackers to compromise authentication tokens or assume other users’ identities.
Broken Object Property Level Authorization: Inadequate authorization controls at the property level, allowing attackers to gain unauthorized access or modification of object properties.
Unrestricted Resource Consumption: Lack of resource and rate limiting, leading to denial of service (DoS) attacks or excessive resource usage.
Broken Function Level Authorization : Missing or ineffective authorization checks on API functions, allowing unauthorized access to sensitive operations.
Unrestricted Access to Sensitive Business Flows: Exposure of critical business processes through the API without proper protection, enabling unauthorized actions or data manipulation.
Server-Side Request Forgery (SSRF): Vulnerabilities allowing attackers to force the API server to make requests to arbitrary internal or external systems.
Security Misconfiguration: Errors or oversights in the configuration of the API or its infrastructure, such as default credentials or exposed debugging endpoints.
Improper Inventory Management: Lack of visibility and control over API versions and deployed assets, leading to potential vulnerabilities in outdated or unused endpoints.
Unsafe Consumption of APIs: Client applications consuming APIs without proper validation or sanitization of data, opening the door for injection attacks and other vulnerabilities.
Authentication and Authorization Weaknesses
Authentication and authorization are fundamental pillars of API security. However, they are also common areas where vulnerabilities arise and are exploited. Here are some specific weaknesses to be aware of:
Weak Passwords: Easily guessable or short passwords can be quickly cracked by attackers.
Lack of Multi-Factor Authentication (MFA): Relying solely on passwords for authentication leaves APIs vulnerable to credential theft.
Insecure Token Management: Improperly generated, stored, or transmitted tokens can be intercepted or stolen.
Role-Based Access Control (RBAC) Misconfiguration: Incorrectly assigning roles or permissions can give users more access than they should have.
Inadequate Session Management: Weak session management can allow attackers to hijack legitimate user sessions.
Lack of Input Validation: Failing to validate input, especially for security credentials, can lead to injection attacks or other forms of data manipulation.
By understanding these risks and vulnerabilities, you can proactively implement security measures to protect your APIs from these issues. Of course, since many of these issues are well-known, there are many ways to solve them and prevent them from becoming a problem in your APIs. In the next section, we will explore best practices for securing your APIs and mitigating these risks.
Securing Your API: Best Practices
With the complexities that come with securing APIs, best practices for API security cover everything from automated testing and monitoring at the code level to adding pieces of infrastructure, such as API gateways, to mitigate risks. We won’t dive into an extensive list, but let’s take a look at some staples you should definitely consider when securing APIs.
Use API Discovery to Understand the Full Picture
Before you can secure your APIs, you need to know what APIs you have and where they reside. API discovery tools , like the one included in StackHawk , automatically scan your network, code repositories, and even runtime traffic to identify all APIs, including hidden or shadow APIs that might have been forgotten or undocumented.
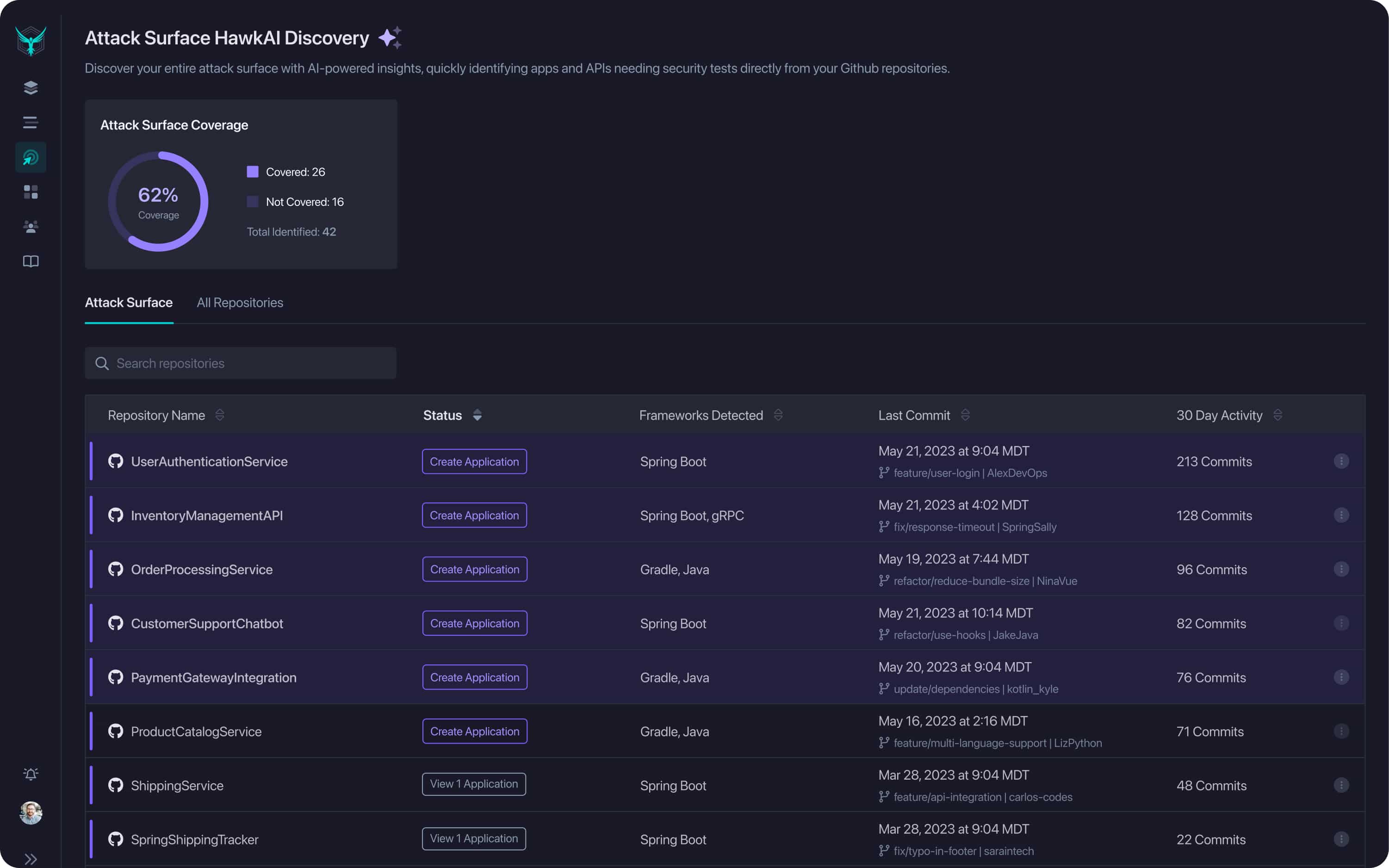
Understanding the full scope of your API landscape is essential for effective risk assessment and security planning. It allows you to:
Identify all potential attack surfaces: Uncover hidden endpoints, outdated versions, or misconfigurations that could be exploited.
Prioritize security efforts: Focus on the most critical APIs that handle sensitive data or perform essential functions.
Ensure comprehensive security coverage: Verify that all APIs are protected by appropriate security measures, including those you may not be aware of.
Leverage Automated Security Testing
Manual security testing can be time-consuming and error-prone. Automated security testing tools, like StackHawk’s dynamic application security testing (DAST) engine , can quickly and efficiently scan your RESTful, SOAP (Simple Object Access Protocol), RPC (Remote Procedure Call), and GraphQL APIs for vulnerabilities, including those listed in the OWASP Top 10 . Combining multiple automated api testing methods, such as also using a platform like Snyk’s static application security testing (SAST), can help to automate coverage from multiple angles.
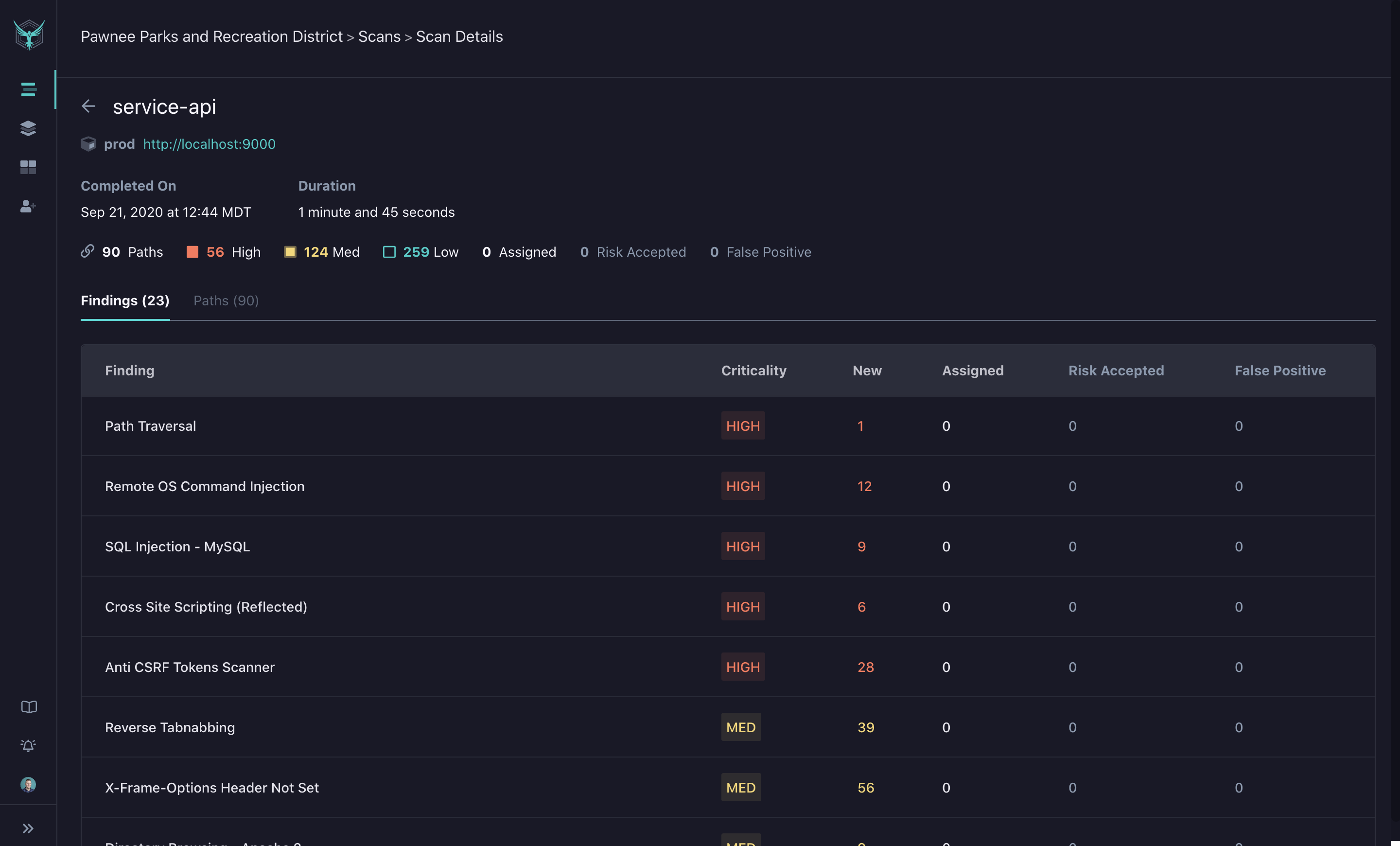
By integrating automated security testing into your development pipeline, you can:
Catch vulnerabilities early: ” shift left ” and identify and fix security issues before they reach production.
Reduce the risk of human error: Automate repetitive tasks, especially by running tasks in CI/CD pipelines, and ensure consistent testing coverage on every commit, pull request, or deployment.
Improve security posture: Continuous testing helps detect new vulnerabilities and adapt your security measures accordingly.
Implement Secure Authentication and Authorization
Robust authentication and authorization mechanisms are essential for controlling access to your API and preventing unauthorized actions. Consider adding the following measures to your API auth:
Strong passwords and MFA: Enforce the use of strong passwords and implement multi-factor authentication wherever possible.
OAuth 2.0 or OpenID Connect: Use industry-standard protocols for secure token-based authentication and authorization through platforms like Okta and Auth0.
Role-Based Access Control (RBAC): Define granular permissions based on user roles to limit access to sensitive resources.
JWT (JSON Web Tokens): Use JWTs for stateless authentication and authorization, ensuring secure transmission of claims and user information.
Use HTTPS and Rate Limiting to Prevent Abuse
Always encrypt API traffic using HTTPS to protect data in transit and prevent eavesdropping or tampering. Additionally, rate limiting should be implemented to restrict the number of API requests or calls an API client can make within a given timeframe. This can help mitigate denial of service attacks and prevent abuse. One of the easiest ways to do this is to integrate your APIs with an API gateway like the ones offered by Kong, Tyk, or WSO2.
API Key Management and Secure Data Handling
Another functionality offered through API gateways, developers can protect API keys by storing them securely in a key management platform and rotating them regularly. Never embed API keys directly in code, especially when committing the code to public repositories, or transmit them in plain text. Implement strong encryption for sensitive data at rest and in transit, and follow secure coding practices to prevent vulnerabilities like injection attacks.
Regular Security Assessments and Monitoring
Make security an ongoing process. Regularly assess your API’s security strategy and posture using tools like StackHawk to identify new vulnerabilities and other tools to help monitor for suspicious activity in API traffic and infrastructure access. Keep your API infrastructure and dependencies up to date to patch known security flaws.
By adhering to these best practices and leveraging tools like StackHawk’s API discovery and DAST capabilities , you can proactively secure your APIs, protect sensitive data, and ensure the reliability of the applications that depend on your APIs.
Conclusion
API vulnerabilities pose a significant threat to modern software. By understanding the API attack surface, recognizing common attack vectors, and proactively implementing best practices, you can effectively mitigate these risks and safeguard your valuable assets.
API security is an ongoing effort, not something you set and forget. API Developers and the teams that support them must stay vigilant, leverage powerful tools like StackHawk to continuously monitor and improve their API security posture, and empower their development teams to build secure applications.
Ready to take the next step in understanding your API attack surface and securing your APIs? Try out StackHawk today to leverage DAST and API Discovery to up your API security posture.